Southeast Asia is a rapidly growing market for financial institutions, and is increasingly relying on mobile phones to onboard customers digitally. In 2021, there are still 174 million adults who lack bank accounts and credit cards, making up 27.10% of the total regional population. This is a tremendous leap when compared to the 50% take-up rate in 2018 .
This represents immense demand for digital financial services throughout the pandemic, with little signs of slowing down. Services such as digital lending, e-wallets still help address existing financial issues faced by the public.
Hence, accessibility is the key determining factor within this digital race, and mobile phones are the best tools for the job – with mobile penetration rates exceeding 100% in countries like Indonesia, Vietnam, the Philippines and more . The traditional KYC process is no longer viable in today’s increasingly digitalised world. Accessibility can only be unlocked through the power of digital identity verification provided by the latest eKYC solution.
User Onboarding Risks
However, Innov8tif has received reports of high user onboarding risks through mobile channels. From a user’s point of view, these apps follow the standard procedure of capturing facial images and identity documents. However, these ID verification captures do not have to be valid to pass through security checks. Ultimately, this flaw in the face verification process can lead to cases of identity fraud, which is very common in any financial institution.
For instance, we have found that certain apps accept photocopied identity documents as proper submissions. There are also others that do not require the captured face to match the profile photo displayed on the customer identity card.

Our internal report shows that these high-risk apps only incorporate three modules for eKYC purposes:
- Facial capture
- Document Capture
- Optical character recognition (OCR) for text extraction
Although sufficient for genuine user sign-ups, such systems are prone to abuse and security vulnerabilities. This can be detrimental to a financial institution and regular users, not to mention the regulatory compliance risks associated with them.
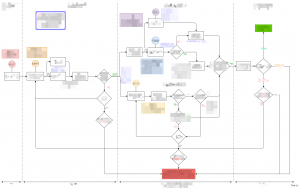
A well-established eKYC journey is exponentially more complex, with layers of checks and balances. It is a fine balancing act of delivering a streamlined customer journey for valid users, while not compromising on security for fraudulent sign-ups.
Common spoofing Techniques

Facial Recognition Capture
Presentation attacks are the most commonly employed form of spoofing, whereby fraudsters present false identities to deceive facial recognition systems. Presentation attacks can come in two forms: Static 2D and Static 3D.
- Static 2D attacks are relatively simple and use two-dimensional flat objects such as photos, paper, or masks to trick the facial recognition system. However, more sophisticated 2D attacks use smartphone or tablet screens to flash images in sequence to mimic live movement.
- Static 3D attacks are more complex and employ the use of 3D printed masks, sculptures, or facial reproductions. These attacks can be more challenging to detect, as they provide a physical depth that makes them appear more realistic to the system.
ID Capture
- Utilising black and white photocopies of the document
- Photoshop and text replacement attempts
- Physical tampering
Importance of Verification
At its core, eKYC is process automation aimed at replacing the traditional KYC process. Even today, traditional KYC practices involve meeting the applicants face-to-face, verifying if the documents are legitimate, and entering applicant details into a digital record. These processes can be further enhanced through machine learning algorithms to reduce inconveniences and improve accuracy.
An eKYC process that does not factor in document or applicant legitimacy needs to grapple with the following challenges:
- Fraud management The lack of verification services opens up the floodgates to fraudulent or bot sign-ups. For non-essential accounts, this could lead to abuses in sign-up benefits, such as free gifts or coupons, nullifying a portion of genuine marketing efforts. In the case of the financial industry, however, these accounts can be used for a far nefarious purpose – setting up mule accounts which can be used to accept and move ill-gotten funds. Mule accounts can also be set up through identity theft – which is already a signal of a flaw in the initial kyc process.
- Sanctity of customer database In any business, a healthy and well-established customer database is one of the company’s greatest assets. Fraudulent and bot sign-ups that insert themselves alongside genuine customers muddies the sanctity of such a customer database. This issue is more detrimental to public-listed companies, where investment decisions are based on the health of the business, which includes accurate statistics around customer databases.
- Lead to further exploits The ability to sign up accounts without proper verification represents a gap within the bank’s security, which can be further exploited to gain deeper level access. Tactics may range from applying social engineering techniques to support staff members, to mass bot attacks targeting the sign-up process. Exploits do not necessarily have to be security-centric either. Having a fraudulent bank account allows bad players to establish credit scores, apply for loans, purchase high-ticket items and more, all the while under the guise of anonymity.
How Innov8tif manages verification
At Innov8tif, we have developed proprietary biometric authentication solutions aimed at providing verification services in tandem with eKYC processes.

OkayDoc is EMAS eKYC’s document verification API which helps determine if a submitted document is authentic or otherwise. It does so by detecting abnormalities within the document itself, such as landmark placements, font type and size, microprint detection, hologram checks, and more.

OkayLive refers to the liveness detection feature within the facial recognition process – ensuring that the selfie captured is taken from a live human being. We utilise passive liveness detection which does not require users to perform actions such as nodding or turning their heads to prove their liveness. It supports a wide range of user base, including hijab wearers.
Looking to learn more about identity verification? Do reach out to [email protected] or tap into our API today via our newly launched EMAS eKYC API OnDemand Portal.