EMAS CIDA — how we architect identity assurance
How we package identity-proofing, due diligence, and authentication into a single architecture that fits your market, regulators, and integration model.
Three pillars, one framework
CIDA is Innov8tif's umbrella for end-to-end identity assurance. Each pillar maps to a feature category in our wiki and to specific components in EMAS eKYC.
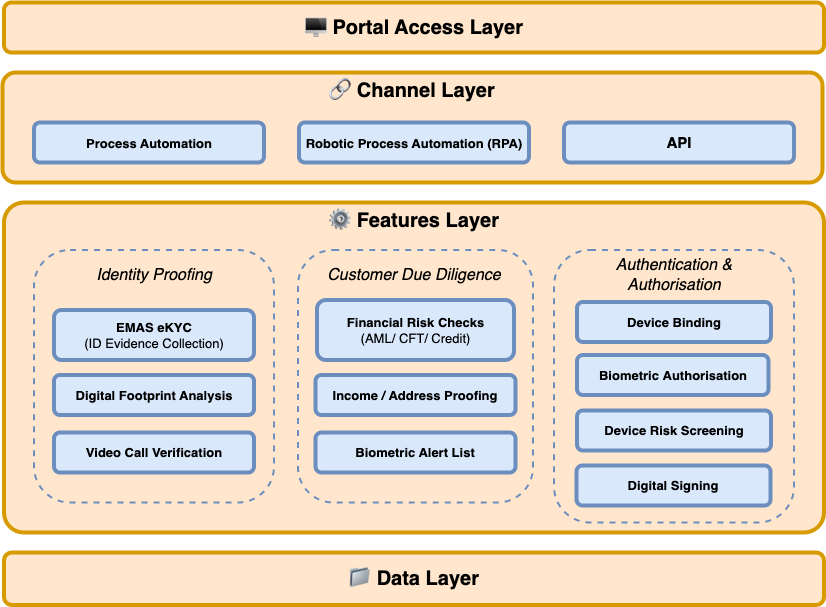
- Identity Proofing
- Document verification, OCR data extraction, face matching, and liveness detection. Confirms the user is who they claim to be at onboarding.
- Customer Due Diligence
- Sanctions, PEP, and adverse-media screening; risk scoring and ongoing monitoring. Confirms it is safe to do business with this user under regulatory rules.
- Authentication & Authorization
- Step-up authentication, biometric reauthentication, and session-level controls. Confirms returning users continue to be the rightful account holder.
Identity Proofing
Verify who someone claims to be at the moment of onboarding.
- · ID capture (OCR, NFC chip read)
- · Liveness detection
- · Facial matching (1:1 to ID photo)
- · Document authentication
Wiki category: identity-verification
Customer Due Diligence
Screen and assess risk after the identity is proven.
- · AML / CFT and sanctions screening
- · Credit scoring and bankruptcy checks
- · Income and address proofing
- · Biometric alert lists
Wiki category: user-screening
Authentication & Authorization
Maintain identity assurance after onboarding for the lifetime of the account.
- · Device binding (MFA on a trusted device)
- · Digital signatures (SigningCloud)
- · Deepfake and injection-attack detection
- · Device risk screening
Wiki category: additional-verification
The EMAS eKYC verification pipeline
Five sequential stages run for every onboarding. Results aggregate into a single scorecard.
OkayID
Captures identity-document data via OCR and NFC chip read.
OkayLive
Confirms the person is real and present — not a photo or replay.
OkayFace
1:1 facial match between live capture and ID-document photo.
OkayDoc
Authenticates the document — layout, security features, tampering.
Scorecard
Aggregates all checks into Clear / Cautious / Suspicious.
Backend orchestration runs through the EMAS HIP Portal — a single integration point that returns the aggregated IDV result to your onboarding channel (mobile, web, or desktop).
One scorecard, three outcomes
Configurable rules per market. The scorecard returns a single decision your onboarding flow can act on immediately.
Clear
User satisfies pre-defined rules. Onboarded automatically — no manual review.
Cautious
Critical checks pass; secondary checks flag (often poor image quality). Routes to manual verification.
Suspicious
Pre-defined rules fail. Onboarding declined — potential fraud attempt.
The bundle of products
EMAS eKYC — what's in the bundle
EMAS CIDA describes how. EMAS eKYC is what you actually integrate. See the components, supported documents, and integration patterns.
Explore EMAS eKYC
See CIDA running in your environment
A 30-minute walkthrough covers the framework, integration patterns, and a live verification flow.