eKYC: a Beginner's Guide
How traditional KYC works
n nnConventionally, users need to physically visit an office branch and submit a government-issued ID document. Employees need to personally verify the authenticity of the ID document and the user’s identity on-site. nnThis represents two major problems:nn1) Increased customer onboarding costs — It is expensive to maintain the upkeep of physical office spaces and human resources. Not to mention, digitising customer information through paper application requires manual data-entry work. Physical offices are also restricted to serving a certain geographic radius, representing opportunity costs. nn2) Damaged customer experience — Many physical branches are only available during office hours, and making multiple personal appointments can be frustrating. Preparing physical documents and printed copies is not only inconvenient, but generates paper wastes as well. n
nnConventionally, users need to physically visit an office branch and submit a government-issued ID document. Employees need to personally verify the authenticity of the ID document and the user’s identity on-site. nnThis represents two major problems:nn1) Increased customer onboarding costs — It is expensive to maintain the upkeep of physical office spaces and human resources. Not to mention, digitising customer information through paper application requires manual data-entry work. Physical offices are also restricted to serving a certain geographic radius, representing opportunity costs. nn2) Damaged customer experience — Many physical branches are only available during office hours, and making multiple personal appointments can be frustrating. Preparing physical documents and printed copies is not only inconvenient, but generates paper wastes as well. nWhat is eKYC?
neKYC can help address many of the shortcomings above. In short, eKYC is the process of digitally verifying a customer’s identity through the use of automated, AI-driven solutions. nnIt does so via a combination of the following authentication factors:n- n
- Something the user possess (ID card, registered phone number) n
- Something the user knows (PIN code, personal information) n
- Something the customer is (Biometric data) n
What the user sees
nWhat businesses see
n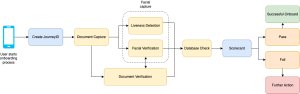 nnThere is no one standardised way of creating proper eKYC workflow, but the example above is a generic example used for most applications. At Innov8tif, our flagship product EMAS eKYC contains all the necessary components to build a robust eKYC system:nnnnnnnnnnnnnnnnnnnnnnnnnnnnnnnnnnnnnnnnnnnn
nnThere is no one standardised way of creating proper eKYC workflow, but the example above is a generic example used for most applications. At Innov8tif, our flagship product EMAS eKYC contains all the necessary components to build a robust eKYC system:nnnnnnnnnnnnnnnnnnnnnnnnnnnnnnnnnnnnnnnnnnnn| Function | EMAS eKYC Component | Description |
| Create Journey ID | HIP Portal | Each signup attempt generates a unique JourneyID, which is tracked and stored on the HIP portal. |
| Document Capture | OkayID | The user first scans their ID document. Personal details are automatically captured and collected using optical character recognition (OCR) technology. |
| Liveness Detection | OkayLive | The user then captures a selfie for authentication purposes. OkayLive ensures the user is a live human being, preventing common spoofing techniques used by fraudsters, such as using digital screens, printed photos etc. |
| Facial Recognition | OkayFace | The user’s facial features are analysed and compared to the profile image located on the ID card —ensuring that the user is indeed the ID card’s owner. |
| Document authentication | OkayDoc | The ID document is checked for authenticity — preventing common spoofing techniques such as photocopied documents, forgery, photoshop attempts etc. It also checks for signs of tampering, such as weird fonts, misplaced landmarks, hologram detection and so on. |
| Database Check | OkayDB | The curated information is then checked against an existing database. Background checks include criminal records , bankruptcy status, politically exposed person (PEP), suspicious previous signup attempts, and more. |
| Scorecard | HIP Portal | The system determines how legitimate a user is by generating a confidence score. Clients have the option to manually approve/reject applicants and generate regular reports, complete with an audit trail. |
Why is eKYC important?
nCybercrimes are a growing issue in ASEAN, especially in sectors that do not have mature security measures in place. Companies are one of the biggest victims of cybercrime, losing about US$20 billion to synthetic identity-related attacks in 2020 alone. Another report shows that bad bots make up 40% of Singapore’s internet traffic, surpassing even the United States. False user registration is not only a nuisance, but a legitimate security threat. nnWith eKYC, companies can:n- n
- Improve customer database integrity n
- Provide borderless 24/7 services n
- Cultivate higher-quality users n
- Mitigate monetary loss n
- Boost stakeholder and customer confidence n
- Comply with regulation n
- and more! n
nn nnEKYC solutions had always been associated with the banking, financial and telecommunications sector. However, digital businesses today have gained more exposure and understand the value of ID Assurance services. In recent years, we have onboarded customers from industries such as human resources, logistics, local governments, e-commerce, internet providers, and more.nnInterested to learn more about eKYC and ID assurance? Get in touch with us at sales@innov8tif.com!
Related articles

Fraud Prevention Best Practices: Staying Ahead in the Digital Age
Fraud has evolved into one of the most pressing challenges for businesses in the digital age, specifically in industries where trust and identity verification are critical, such as banking, insurance, telecommunications, and e-commerce. Fraudsters are after one thing, and one thing only: your perso
Fraud Prevention in the Digital Age: How AI is Transforming the Fight Against Scams
The onset of the digital age has ushered in remarkable innovations that we never would have thought possible a decade ago. Everything, from the way we work to the way we live our daily lives, has been drastically streamlined by technological advances. However, this progress comes with a double edge
The Digital Deception: How to Spot, Prevent, and Fight Fraud in a Hyper-Connected World
Fraud is no longer just a distant threat in this digital age — it’s a reality that could impact you, your family, or your business at any moment. Think about it: how often do you shop online, check your bank account on your phone, or share personal details over email? These everyday actions, while
